Key Highlights
- CertiK flagged an attack on the Hyperbridge gateway contract on Ethereum, where the attacker forged a cross-chain message from Polkadot. By deploying a master + helper contract and submitting fake state proofs, they bypassed verification to steal admin/minter rights over the official DOT token contract.
- The attacker minted ~1 billion DOT tokens (roughly 2,805× the reported ERC-20 supply of 356K tokens), immediately swapped them via OdosRouter and Uniswap V4 for 108.2 ETH, and sent the funds to their EOA.
- This is the second exploit of the same system within hours — an earlier one resulted in ~$12K in MANTA and CERE tokens, with the vulnerability lying in insufficient verification of state proofs in Hyperbridge’s ISMP pipeline.
Blockchain security firm CertiK has flagged a fresh exploit targeting the Hyperbridge gateway contract on Ethereum. According to the alert, an attacker successfully forged an incoming cross-chain message to seize control of the Polkadot (DOT) token contract deployed on Ethereum.
The incident unfolded through Hyperbridge’s ISMP (Interoperable State Machine Protocol), which facilitates secure messaging between chains like Polkadot and Ethereum. The attacker deployed a master contract and a helper contract in a single transaction.
The helper then submitted forged state proofs to the vulnerable HandlerV1 contract (address: 0x6c8…4E6D64), bypassing verification checks. This allowed a malicious “ChangeAssetAdmin” action to be executed via the TokenGateway.onAccept() path, transferring admin and minter privileges of the DOT token contract (0x8d…8F90b8) to the exploiter.
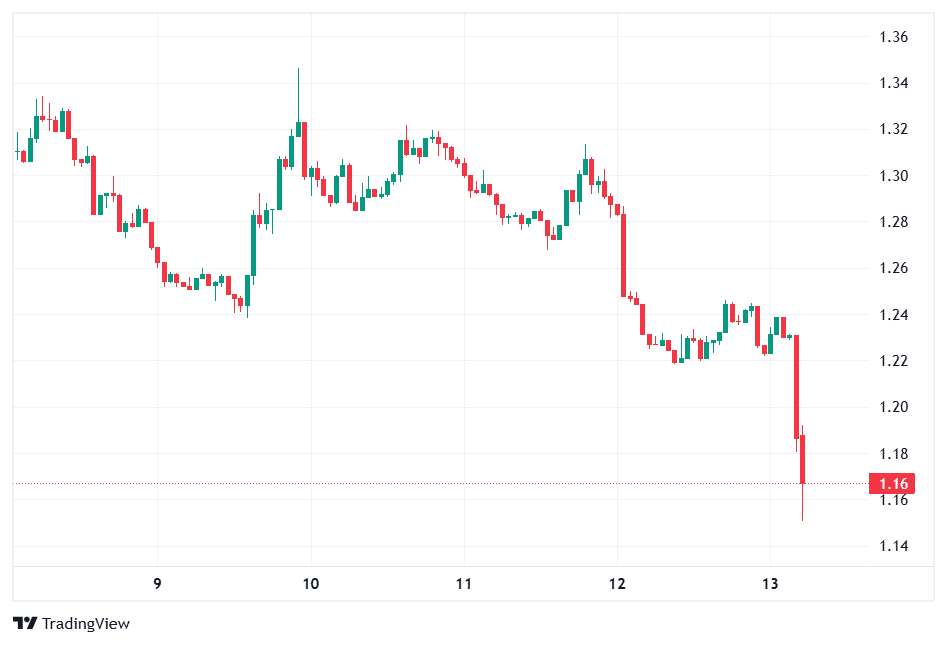
Following the exploit, DOT token price dropped by roughly 4.8% to $1.16—as per CoinMarketCap data.
Yet another token mint exploit
Data from Etherscan, the blockchain explorer for Ethereum, shows that the attacker minted a staggering 1 billion DOT tokens—approximately 2,805 times the reported total supply of around 356,000 tokens (ERC-20) on Ethereum.
The newly minted tokens were immediately swapped through OdosRouter and Uniswap V4 pools for roughly 108.2 ETH, which was forwarded to the attacker’s externally owned account (EOA: 0xc513…f1f8e7) and funds remain in this wallet as of publishing.
At current prices, the profit stands at approximately $237,000. Despite such a huge token supply (1 billion DOT), the actual amount scale in this exploit remains modest due to low liquidity on Hyperbridge pools. The fallout would have been much larger if tokens were bridged to native DOT on the Polkadot network.
This marks the second exploit of the same system on the same day. An earlier attack reportedly drained around $12K in MANTA and CERE tokens using a similar vector. The root cause appears to stem from insufficient verification of state proofs in the ISMP pipeline, enabling unauthorized governance actions on connected token contracts.
Hyperbridge, developed by Polytope Labs, positions itself as a secure, trust-minimized interoperability layer that relies on cryptographic proofs from source chains rather than multisig committees.
The project has previously emphasized resistance to common bridge hacks, which have collectively cost the ecosystem billions. However, today’s incident highlights ongoing challenges in cross-chain messaging security, particularly around proof validation and admin control in token gateways.
As of now, no official statement from Hyperbridge or Polytope Labs has been widely circulated regarding mitigations, pauses, or fund recovery efforts.
This is a developing story and more information will be added as the event unfolds.
Also read: WLFI Drops 15% After $75M DeFi Borrow Sparks Concerns