Key Highlights
- Attackers use throwaway accounts to mass-tag OpenClaw stargazers in fake issues, promising $5K $CLAW tokens and redirecting via share.google links to token-claw[.]xyz, a fake openclaw.ai clone that drains wallets.
- The project rocketed past 250,000 GitHub stars in early 2026, drawing ClawHavoc supply-chain poisoning (340+ malicious ClawHub skills with stealers), critical bugs (CVE-2026-25253 RCE, ClawJacked hijacking), exposed instances, fake npm RATs, and rug-pull memecoins like $CLAWD.
- This phishing reflects rising attacks on agentic AI tools, exploiting hype for phishing, supply-chain tampering, and wallet drainers; OX Security advises blocking domains, ignoring tags, verifying URLs, and revoking approvals.
Developers tied to the explosive OpenClaw AI agent project are under siege again, this time from a targeted phishing operation exploiting GitHub to push fake $CLAW token airdrops and drain crypto wallets.
A latest report from researchers at OX Security exposed the active campaign on March 18, 2026, highlighting how attackers are weaponizing the project’s massive community to steal funds.
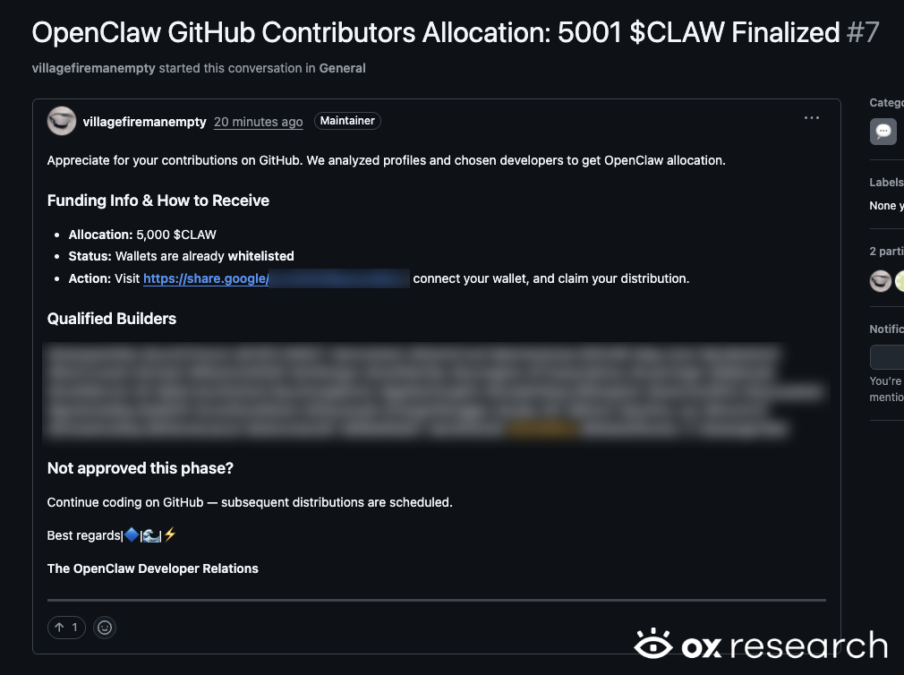
In this novel method, attackers spun up throwaway GitHub accounts and open issue threads in their own repositories, mass-tagging dozens of users. It especially targeted those who starred in OpenClaw-related repos.
The posts claims recipients earned a $5,000 allocation of $CLAW tokens for their contributions, urging them to claim it via a link. Those links, often hidden behind share.google redirects, leads to token-claw[.]xyz, a near-perfect clone of the real openclaw.ai site.
This further leads to a fake page with a big “Connect your wallet” button supporting MetaMask, WalletConnect, Trust Wallet, OKX, and Bybit. While connected, it triggers obfuscated JavaScript in a file called eleven.js and pulls wallet addresses, balances, and transaction data.
The data is later shipped to a command server at watery-compost[.]today, and queues transfers to the attacker’s address: 0x69…aFCf5. A cleanup routine later wipes browser traces and leaves behind nothing in history.
At the time of publication, no confirmed thefts have surfaced and the attacker wallet remains vacant with no activity, but the tactic preys on trust in GitHub notifications and OpenClaw’s hype.
OX Security reported the main fake account vanished quickly after launch, but copycats keep popping up.
OpenClaw’s meteoric rise draws relentless attacks
Launched as Clawdbot late last year, rebranded through Moltbot to OpenClaw, the self-hosted AI assistant shattered records in early 2026, rocketing past 250,000 GitHub stars faster than any project in history. That visibility turned it into a magnet for abuse.
By February, researchers uncovered ClawHavoc—a supply-chain poisoning wave dumping over 340 malicious skills onto ClawHub, the official marketplace. Many posed as crypto tools or productivity add-ons but installed Atomic macOS Stealer variants or reverse shells to grab wallets, browser logins, SSH keys, and keychains.
With these developments, high-severity bugs piled on. CVE-2026-25253 enabled one-click remote code execution via crafted WebSocket links, stealing auth tokens. Another flaw, ClawJacked, lets malicious sites hijack local instances silently through the browser.
Furthermore, detailed scans revealed tens of thousands of exposed instances running with no authentication, turning personal agents into open backdoors. Fake npm packages mimicking installers delivered RATs, while unauthorized memecoins like $CLAWD pumped briefly on Solana before rug-pulling.
MetaMask’s February security roundup flagged OpenClaw experiments that went sideways, with agents accessing wallets leading to losses. Bing searches sometimes pointed to poisoned repos. The creator endured account hijacks, malware drops from stolen handles, and constant harassment.
Broader 2026 crypto threat landscape
This GitHub phishing fits a grim 2026 pattern where AI hype meets persistent crypto crime. Agentic tools promise autonomous tasks, including wallet interactions, creating fresh attack surfaces. It sets prime examples on how phishing, supply-chain tampering, and drainers adapt fast and turn community enthusiasm into risk.
OX Security recommends blocking token-claw[.]xyz and watery-compost[.]today, ignoring unsolicited GitHub tags pushing tokens, and double-checking every URL. If a wallet connected recently via a suspicious link, check history, revoke approvals, and consider migrating funds.
OpenClaw maintainers patched known issues, tightened ClawHub vetting, and deprecated insecure defaults, but the project’s scale ensures it stays a prime target. In crypto and AI alike, rapid growth often outruns security, leaving users to stay one step ahead of the next scam.
Also read: Coinbase Commerce Faces Backlash Over ‘Unsafe’ Seed Phrase Tool